WisQuas
Next level vulnerability scanner &
digital footprint discovery
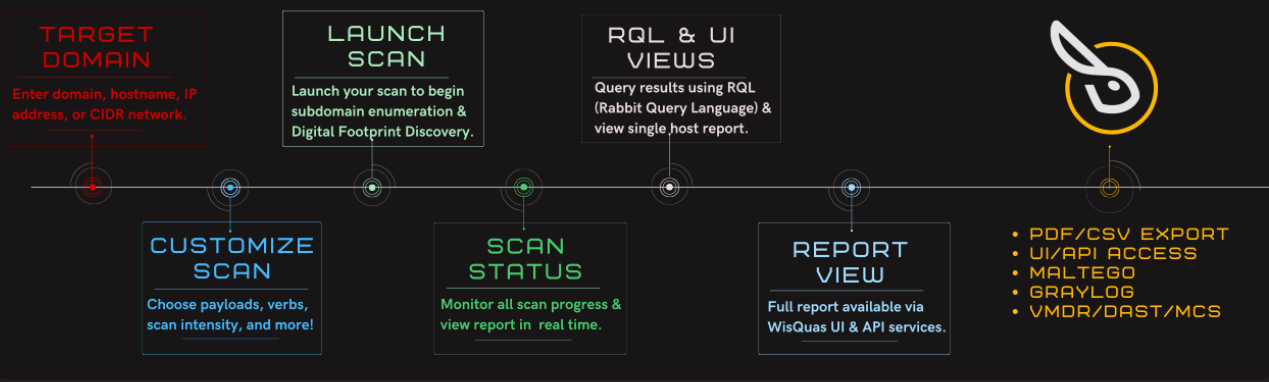
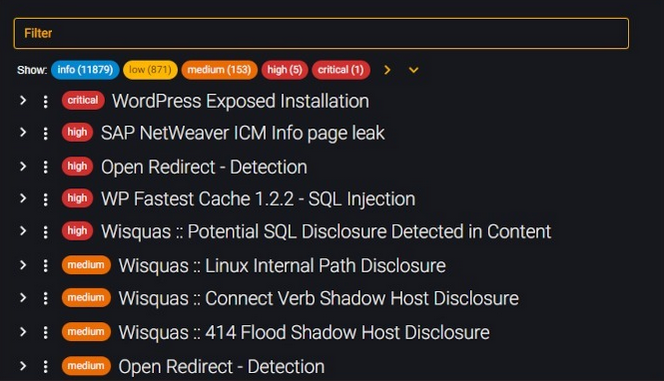
WisQuas® attempts to reveal hidden threats and vulnerabilities around your entire domain and web services by performing ‘Digital Footprint Discovery & Inventory’ along with ‘Vulnerability Scanning & Anomaly Detection’. WisQuas will reveal Exploitable Vulnerabilities, Information Disclosures, Security and Service Misconfigurations, Default Installations, Missing Input Sanitization, and more, using our custom RQL signatures along with utilizing the popular Nuclei Scanner & Framework (WisQuas features and scan information provided below).
- WHOIS lookup on domain names
- Subdomain/Host enumeration & brute-force
- Resolve Hostnames to IP addresses
- ASN/GEO lookup on IP addresses
- Reputation and classification lookups
- Enumeration of payloads, verbs, user-agents, and host headers
- Vulnerability Scanning & Anomaly Detection
- Inventory of all response headers & content
- Results searchable with RQL & API
- Full report access using UI (PDF export), API, Maltego, Graylog
- Scheduled/Continuous Scanning with Monitoring & Alerting
Talk to a rabbit
WisQuas Dashboard & Sample Report
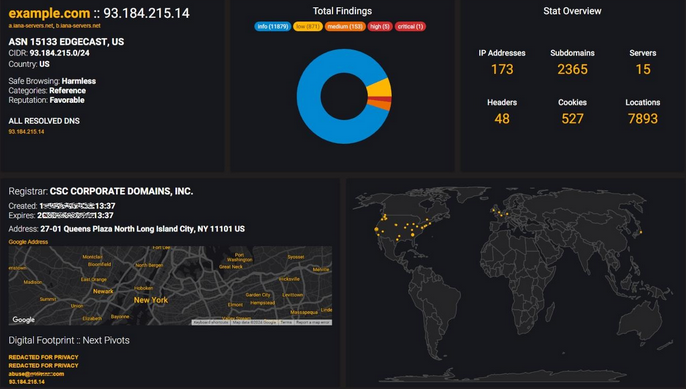
WisQuas Dashboard
Why limit your Vulnerability Assessments and Penetration Testing to a handful of systems during an engagement when you can analyze your ENTIRE DOMAIN!
Findings Table
Perform an all-in-one Threat Landscape Assessment, Vulnerability & Misconfiguration Scan, Digital Footprint Discovery & Inventory, and OSINT Investigation, with WisQuas®.
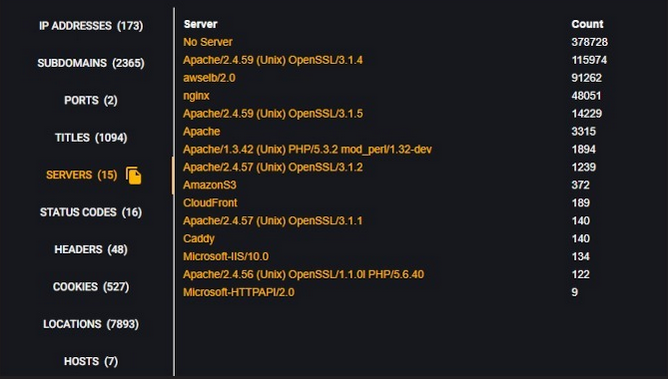
Classification of Domain Attributes
WisQuas® attempts to reveal that which may be hidden, through content discovery, enumeration, and fingerprinting asset around your entire domain and its web services.